What is the name of Check Point collaborative network that delivers real-time dynamic security intelligence to Check Point threat prevention blades?
A. ThreatSpect
B. ThreatWiki
C. ThreatCloud
D. ThreatEmulator
Which of the following is information uploaded to ThreatCloud?
A. Compromised Machine IP Addresses
B. Malware Site IP Addresses
C. Anticipated Attack Methods
D. Sensitive Corporate Data
Sensitive corporate data is uploaded to ThreatCloud:
A. When the administrator manually sends suspected traffic to ThreatCloud for inspection.
B. Never
C. When the administrator configures the sensor to be a SensorNET participant.
D. After the bot attack has been confirmed.
What is the name of the Check Point cloud-driven Knowledgebase?
A. ThreatSpect
B. ThreatCloud
C. ThreatWiki
D. ThreatEmulator
IPS can assist in the discovery of unknown buffer overflow attacks without any pre-defined signatures.
A. False, only the Threat Emulator blade can discover unknown attacks.
B. True, if Zero-Day vulnerability is enabled.
C. False, IPS needs predefined signatures for all functions.
D. True, if Malicious Code Protector is enabled in IPS.
How can SmartEvent be launched out of SmartDashboard?
A. Threat Prevention Tab > Launch SmartEvent
B. Menu SmartConsole > SmartEvent
C. Menu SmartConsole > SmartEvent or Threat Prevention Tab > Analyze and Report
D. SmartEvent has always to be launched via Start > Programs
An end-user calls the helpdesk, complaining that he cannot access a web site. You check the log and see that an IPS signature is dropping his connections. What can you do? Change the signature action to:
A. Bypass
B. Detect
C. Inactive
D. Prevent
This graphic shows traffic being blocked from certain countries.
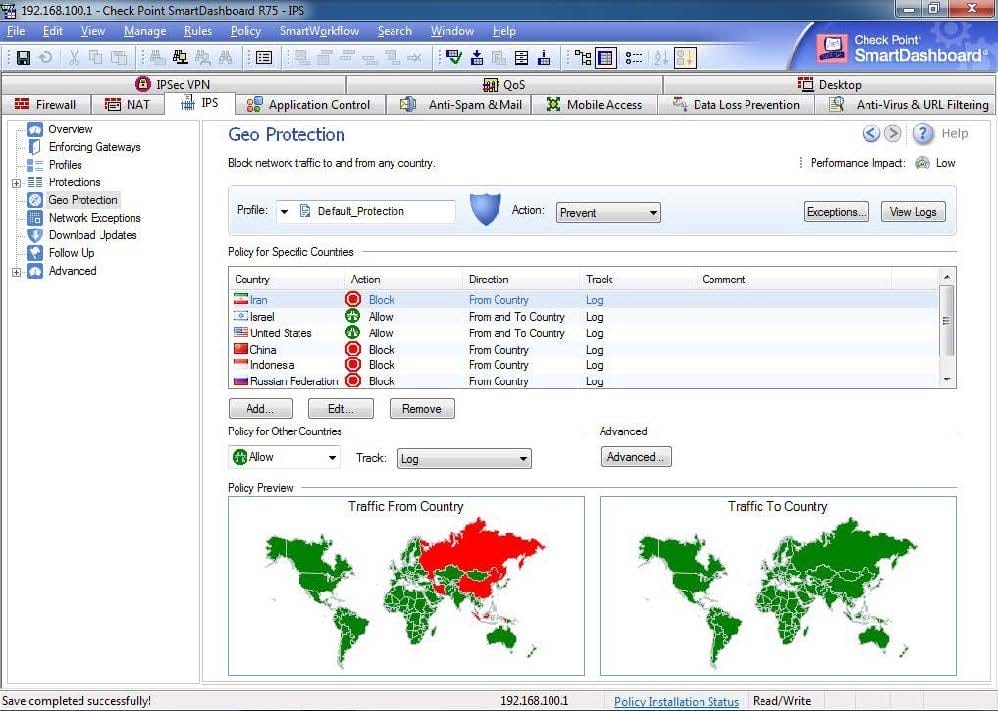
What is the deciding factor for this?
A. The traffic from selected countries is being blocked because of an IPS traffic-type rule in the rulebase
B. The traffic from selected countries is being blocked because it is overloading the Gateway
C. The traffic from selected countries is being blocked due to the GeoProtection ruleset
D. The traffic from selected countries is being blocked due to IPS-detected specific attacks originating there
SmartLog can be used to identify which of the following:
A. Security Policy version control information
B. A list of currently connected users
C. The country of origin of specific traffic displayed on a map
D. The top destination IP addresses of a specific source
Which of the following are valid Boolean search terms that can be used in custom SmartLog queries?
A. And, or, with
B. And, or, not
C. None, Boolean search terms cannot be used in SmartLog.
D. And, or, not, with