A Citrix Architect needs to enable the security of the Virtual Delivery Agent (VDA) by evaluating the `Enable-VdaSSL.ps1 -Enable' script.
Which supported SSL protocol version is least secure when using the default settings of the script?
A. TLS 1.0
B. SSL 3.0
C. TLS 1.2
D. TLS 1.1
E. SSL 1.0
F. SSL 2.0
Scenario: Engineers at a new company developed their product and infrastructure in Microsoft Azure. The engineers have reached out to a Citrix Architect to help design an Azure infrastructure to support publishing applications using the Citrix Virtual Apps and Desktops service. Costs need to be kept to a minimum.
Which Azure virtual machine (VM) series provides the lowest cost per user while also providing good performance?
A. A-series
B. B-series
C. H-series
D. D-series
Scenario: A Citrix Architect is designing and implementing a new Citrix Virtual Apps and Desktops environment. During the kickoff meeting, management advised that their main business driver is to increase user flexibility for internal and mobile employees.
Which two design decisions should the architect make based on the listed business drivers? (Choose two.)
A. Implement a company-wide bring-your-own device (BYOD) initiative.
B. Implement Citrix Files for internal and external collaboration and filesharing.
C. Enhance security settings on internal network hardware and firewalls.
D. Locate user workstations close to the application servers and corporate data.
E. Segment the company network and related functionalities.
What are three things a Citrix Architect should when using thin clones with Machine Creation Services (MCS)? (Choose three.)
A. Storage and virtual machine (VM) migration may be more complex when compared to full clones.
B. Provisioning speed is slower when compared to full clones.
C. Storage fragmentation may occur over time.
D. Storage space should be closely monitored.
E. Higher storage space is required when compared to full clones.
Scenario: A Citrix Architect designing a new Citrix Virtual Apps and Desktops environment needs to determine which endpoints to include. Based on discussions with various departments, the user requirements listed in the exhibit were collected.
Click the Exhibit button to view the requirements.
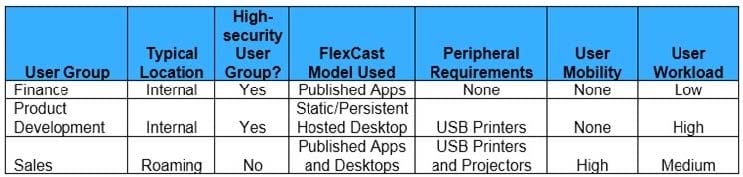
In addition to the user requirements, the architect must address the organizational requirement of minimizing endpoint management effort.
Which endpoint type should the architect use for the Sales Group, based on the requirements?
A. Corporate-owned thin client
B. Bring-your-own device (BYOD) laptop/notebook
C. Corporate-owned smartphone
D. Corporate-owned laptop/notebook
E. Bring-your-own device (BYOD) smartphone
Scenario: A Citrix Consultant is designing a new Citrix Virtual Desktops environment. During the user segmentation process, a Citrix Architect collected a small amount of data about user requirements, but was NOT able to create well- defined user groups.
Which user-segmentation actions should the consultant pursue?
A. Collect user data, define user groups, and identify user requirements.
B. Collect user data, confirm user groups, and identify user requirements.
C. Analyze existing data, define user groups, and confirm user requirements.
D. Analyze existing data, confirm user groups, and identify user requirements
Scenario: A Citrix Architect is implementing a new Citrix Virtual Apps and Desktops environment.
The customer has 3 requirements:
All users must be able to aggregate resources from all Sites.
Both Sites should be treated as 1 equivalent farm set.
User connections should be directed to the New York Site with failover to San Francisco.
Click the Exhibit button to view the StoreFront configurations.
Exhibit 1.
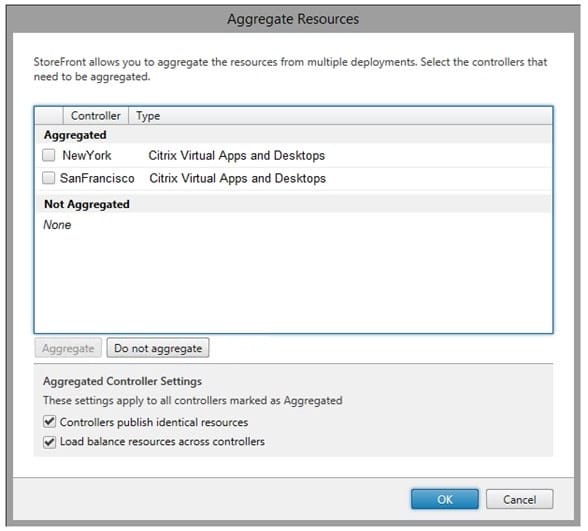
Exhibit 2.
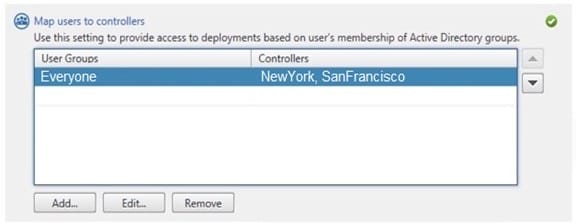
Based on the configurations, requirement 1 is ______________, requirement 2 is ______________, and requirement 3 is ______________. (Choose the correct option to complete the sentence.)
A. met; met; NOT met
B. met; NOT met; NOT met
C. NOT met; met; met
D. met; met; met
E. NOT met; met; NOT met
F. met; NOT met; met
G. NOT met; NOT met; NOT met
Scenario: A Citrix Architect is designing a new Citrix Virtual Apps and Desktops environment. Management has requested dynamic distribution of users between the primary and backup data centers to ensure that all available hardware is utilized during normal operations.
What is the biggest risk the architect should highlight to the customer when designing the profile strategy?
A. Scale-Out File Servers are required to support active-active profile deployments
B. Using Microsoft Distributed File System Replication (DFSR) to replicate user profiles requires significant bandwidth
C. Replicating profiles between the 2 data centers will double storage costs
D. Roaming profiles are NOT supported in active-active Microsoft Distributed File System Replication (DFSR) deployments
Scenario: A Citrix Architect is implementing a new Citrix Virtual Apps and Desktops environment.
The customer has 3 requirements:
All users must be able to aggregate resources from all Sites.
Both Sites should be treated as 1 equivalent farm set.
User connections should be directed to the New York Site with failover to San Francisco.
Click the Exhibit button to view the StoreFront configurations.
Exhibit 1.
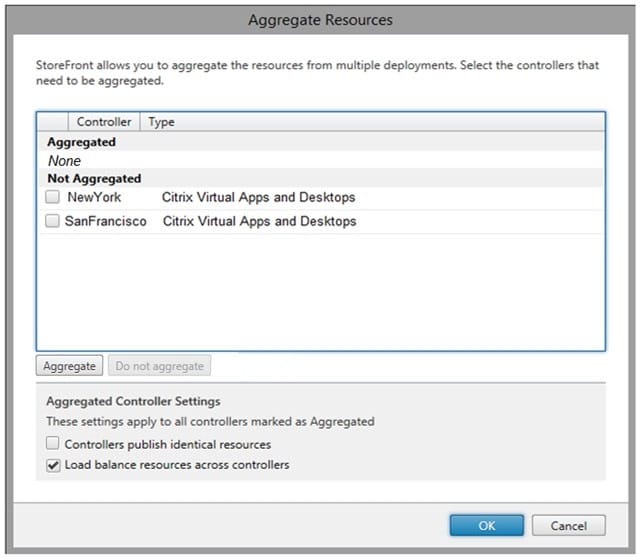
Based on the configurations, requirement 1 is ______________, requirement 2 is ______________, and requirement 3 is ______________. (Choose the correct option to complete the sentence.)
A. met; met; met
B. NOT met; NOT met; NOT met
C. NOT met; met; met
D. NOT met; met; NOT met
E. met; met; NOT met
F. met; NOT met; met
G. met; NOT met; NOT met
Scenario: The IT team of a company needs to mitigate the Hardware Layer to Microsoft Azure. The Virtual Delivery Agent (VDA) machines are manually provisioned within Microsoft Azure. The IT team asks a Citrix Architect for a solution for high availability of existing VDA machines in a single Azure data center. The objective is to be proactive about any hardware failure at Microsoft Azure, so that all virtual machines (VMs) will NOT be affected.
What should the architect recommend the IT team create in Microsoft Azure?
A. Resource group
B. Availability sets with fault domain
C. Availability sets with update domain
D. Availability zones