SIMULATION
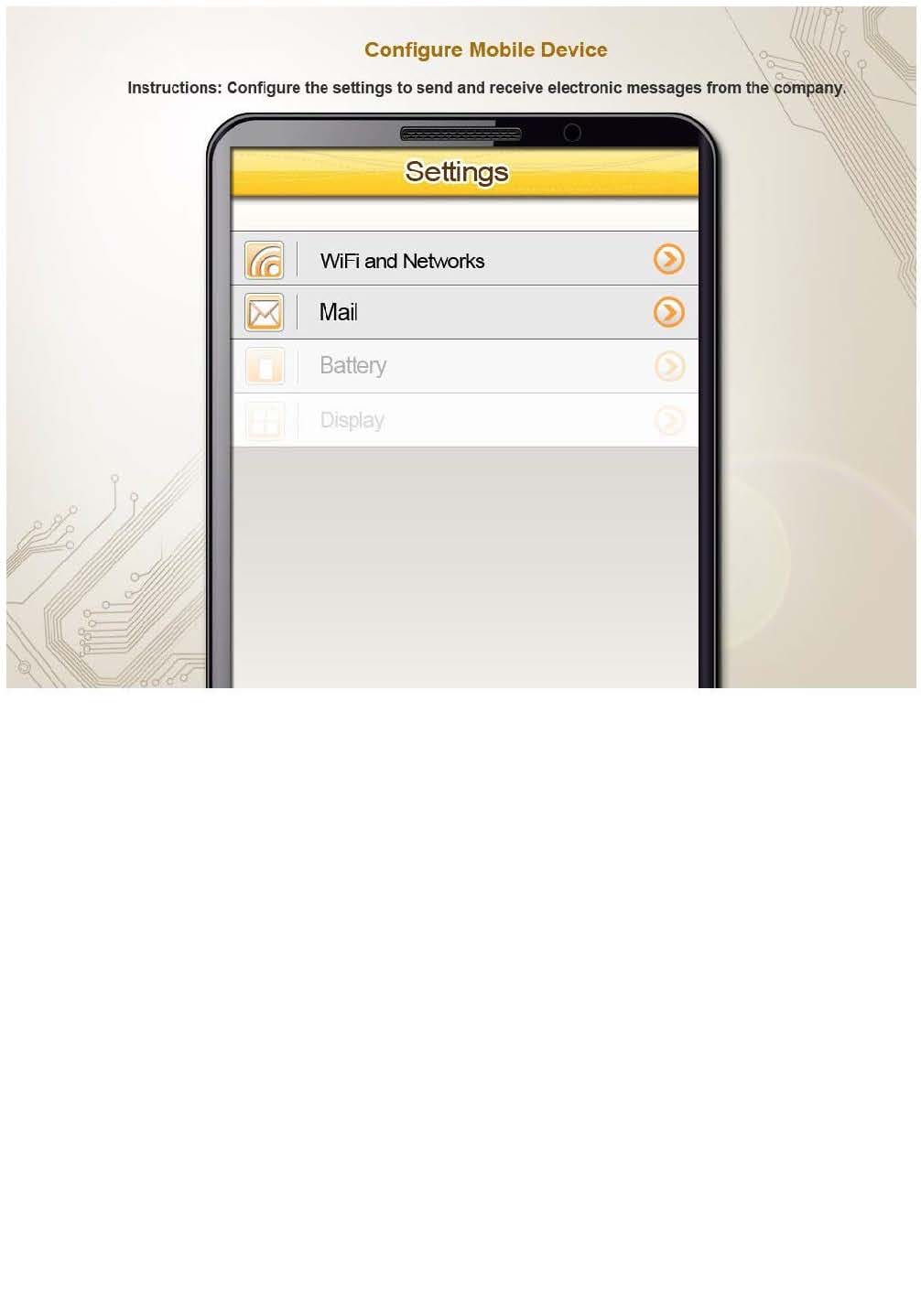
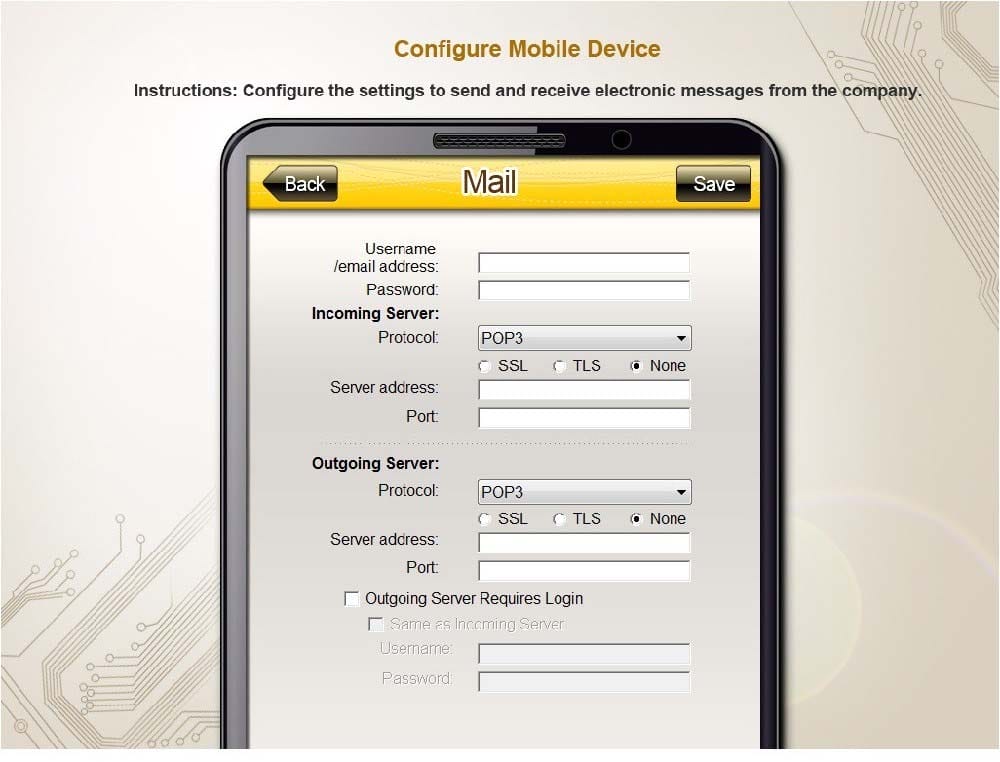
You need to configure your mobile device to send and receive electronic messages from your company. Your mobile device must be able to truly synchronize the message state with your desktop, so that when a message is read on your desktop, it is marked as read on your mobile device. These are the proper parameters:
Email address: [email protected]
Password: P@$$w0rd
Pop.techies.com Port: 110 Security: None
IMAP.techies.com Port: 993 Security: SSL
smtp.techies.com Port: 465 Security: TLS
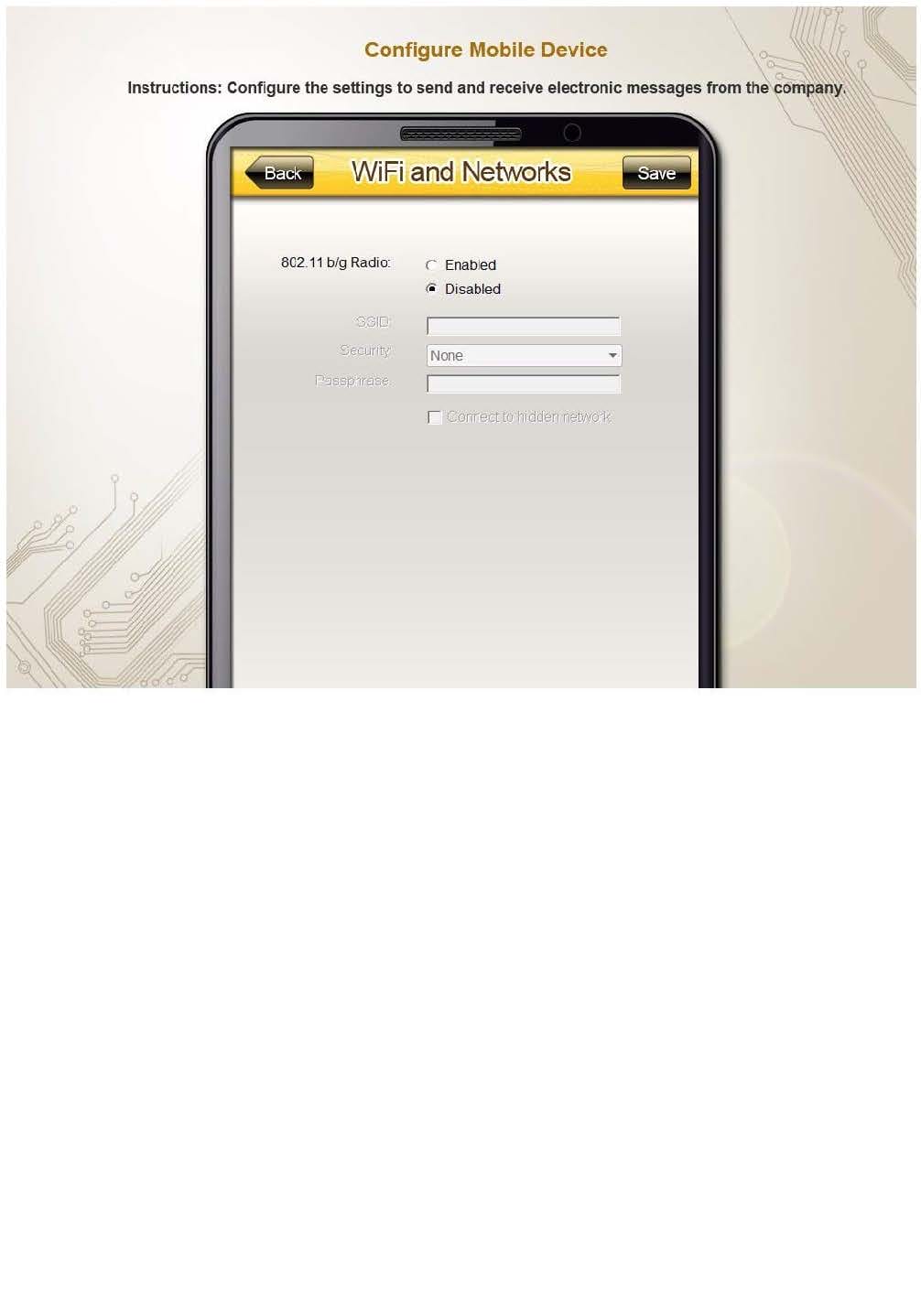
Company SSID: Techies
Security: WPA2
Passphrase: P@$$w0rd
SSID is not broadcasted
Instructions: You are not authorized to use the Company's WLAN. The outgoing server does not require login credentials. When you have completed the simulation, please select the done button to submit your answer.
A user has moved into a building and is installing a new wired network. There is existing cabling throughout the building. The user would like to prevent hardware that they do not own from connecting to the network. Which of the following actions would BEST prevent outside users from connecting?
A. Enable static IPs
B. Disable DNS
C. Disable local proxy server
D. Enable MAC filtering
Which of the following operating systems has the Shake, Peek and Snap features?
A. Windows XP Home
B. Windows 7 Professional
C. Windows XP Professional
D. Windows Vista Business
Which of the following are examples of digital security? (Select TWO).
A. Strong password
B. Privacy screen
C. Badge
D. MAC filtering
E. Mantrap
A user reports an issue of intermittent Read / Write errors occurring on their PC. Which of the following actions would a technician MOST likely take?
A. Run FDISK on the drive
B. Update definitions and run a virus scan
C. Low level format the drive
D. Run CHKDSK on the drive
Which of the following is the correct path to determine the IP address on an iOS device?
A. General> Settings> Wi-Fi> SSID Name> Network> IP address
B. Wi-Fi> SSID Name> Network> IP address
C. Settings> General> Network> Wi-Fi> SSID Name> IP address
D. Location Services> Settings> Wi-Fi> SSID Name> Network> IP address
When connecting a Bluetooth device to a mobile device, which of the following BEST describes the purpose of discovery mode?
A. Allows two Bluetooth devices to connect to each other without a mobile device
B. Disconnects all devices and connects to the closest powered on device
C. Allows a peripheral to be contacted by the mobile device
D. Instructs the phone to seek out all nearby devices and connect to them
Ann reports that printouts from the department laser printer have become faded. She has already replaced the toner cartridge. Which of the following is the MOST likely component causing the faded printing?
A. Transfer roller
B. Fusing assembly
C. Registration assembly
D. Duplexing assembly
Which of the following threats changes system functionality at the operating system level for a malicious purpose by gaining administrative access after being installed by a user?
A. Botnet
B. Trojan
C. Worm
D. Rootkit
What is a common symptom of a problem starting up the Windows 7 operating system?
A. Spontaneous shutdown/restart
B. Invalid boot disk
C. WinRE won't start
D. The optical disc failed
E. Emergency repair disk doesn't boot
F. REGSVR32 has failed