When designing a multi-site NSX deployment, which capability requires Enhanced Linked Mode to function?
A. Creating Universal Transport Zones
B. Creating Universal Logical Switches
C. Cross-vCenter vMotion
D. Registering a Secondary NSX Manager
An administrator needs to perform a configuration backup of NSX. From which two locations can this task be performed? (Choose two.)
A. Directly on the NSX Manager
B. From the vSphere Web Client
C. Using the NSX API
D. Directly on each NSX Controller
An administrator has been asked to provide single failure redundancy. What is the minimum supported number of NSX Controllers needed to meet this requirements?
A. 2
B. 3
C. 1
D. 5
There is intermittent connectivity reported between virtual machines on separate hosts over logical switching.
What command-line tool can be used to test the MTU between two hosts?
A. netstat -1
B. esxcli network ip neighbor list
C. vmkping
D. traceroute
An NSX administrator notices an error during the initial configuration of the SSO lookup service, as shown:
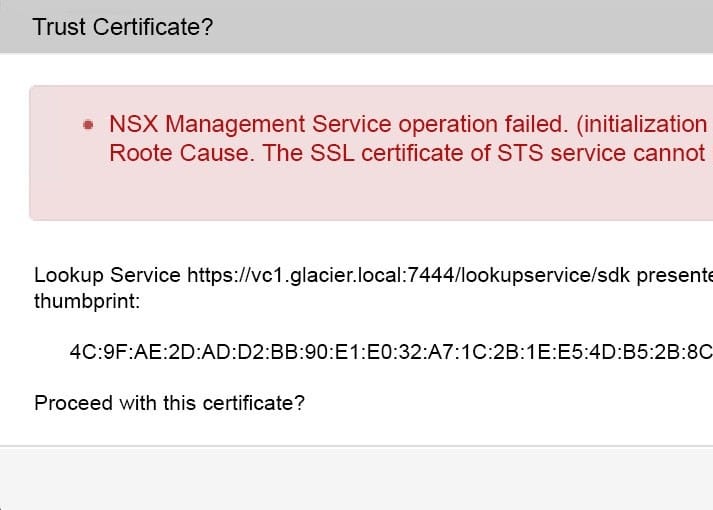
The administrator pulls up the lookup service status, which displays Disconnected.
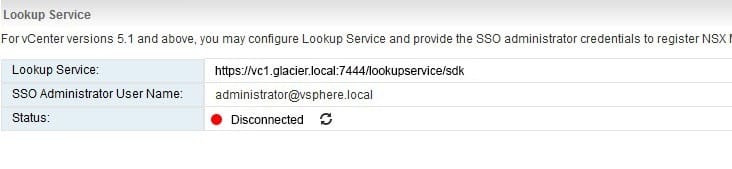
What step should be performed to resolve this issue?
A. Change the Port number from 7444 to 443
B. Change the SSO Administrator User Name
C. Regenerate the SSL Certificate and reboot the NSX Manager
D. Use IP address versus the DNS name in the Lookup Service
What vSphere Distributed Switch security policy allows virtual machines to send frames with a MAC Address that is different from the one specified in the vmx file?
A. MAC Address Changes
B. Failover detection
C. Forged Transmits
D. Promiscuous Mode
A network administrator is troubleshooting an issue and needs to observe an injected packet as it passes through the physical and logical network.
Which tool will accomplish this?
A. Traceflow
B. NetFlow
C. Flow Monitoring
D. Activity Monitoring
Which is a best practice to secure system traffic, ensure optimal performance and satisfy prerequisites for NSX?
A. Configure a single VMkernel and a single distributed port group for all the system traffic.
B. Configure a single distributed port group with a single VMkernel for Management and iSCSI traffic, a separate VMkernel for vMotion and VSAN traffic.
C. Dedicate separate VMkernel adapters for each type of system traffic. Dedicate separate distributed port groups for each VMkernel adapter and isolate the VLANs for each type of system traffic.
D. Dedicate separate VMkernel adapters for each type of system traffic and dedicate separate standard switches for each type of system traffic connected to a single physical network.
Which tool is used to detect rogue services?
A. NSX Logical Firewall
B. NSX Logical Router
C. Activity Monitoring
D. Flow Monitoring
What can be enabled on the vSphere Distributed Switch to monitor IP packets that are passing through a distributed port group?
A. Traffic Marking
B. TraceFlow
C. Traffic Filtering
D. NetFlow