Which of the following are the MOST important risk components that must be communicated among all the stakeholders?
Each correct answer represents a part of the solution. Choose three.
A. Various risk response used in the project
B. Expectations from risk management
C. Current risk management capability
D. Status of risk with regard to IT risk
Which of the following is the BEST defense against successful phishing attacks?
A. Intrusion detection system
B. Application hardening
C. End-user awareness
D. Spam filters
Which of the following interpersonal skills has been identified as one of the biggest reasons for project success or failure?
A. Motivation
B. Influencing
C. Communication
D. Political and cultural awareness
You are the project manager of the HGT project in Bluewell Inc. The project has an asset valued at $125,000 and is subjected to an exposure factor of 25 percent. What will be the Single Loss Expectancy of this project?
A. $ 125,025
B. $ 31,250
C. $ 5,000
D. $ 3,125,000
When performing a risk assessment of a new service to support a core business process, which of the following should be done FIRST to ensure continuity of operations?
A. Define metrics for restoring availability.
B. Identify conditions that may cause disruptions.
C. Review incident response procedures.
D. Evaluate the probability of risk events.
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor's control environment?
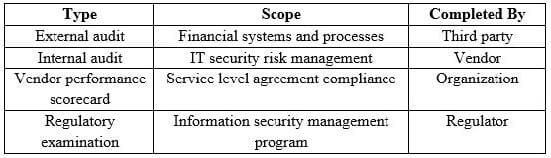
A. External audit
B. Internal audit
C. Vendor performance scorecard
D. Regulatory examination
As part of an overall IT risk management plan, an IT risk register BEST helps management:
A. align IT processes with business objectives.
B. communicate the enterprise risk management policy.
C. stay current with existing control status.
D. understand the organizational risk profile.
Which of the following will BEST help an organization evaluate the control environment of several third-party vendors?
A. Review vendors' internal risk assessments covering key risk and controls.
B. Obtain independent control reports from high-risk vendors.
C. Review vendors performance metrics on quality and delivery of processes.
D. Obtain vendor references from third parties.
After mapping generic risk scenarios to organizational security policies, the NEXT course of action should be to:
A. record risk scenarios in the risk register for analysis.
B. validate the risk scenarios for business applicability.
C. reduce the number of risk scenarios to a manageable set.
D. perform a risk analysis on the risk scenarios.
An organization's internal auditors have identified a new IT control deficiency in the organization's identity and access management (IAM) system. It is most important for the risk practitioner to:
A. perform a follow-up risk assessment to quantify the risk impact
B. verify that applicable risk owners understand the risk
C. implement compensating controls to address the deficiency
D. recommend replacement of the deficient system