A system administrator has created a cluster containing two servers in a same node. The administrator did not select the option Generate unique HTTP ports during the creation of the cluster members. After the cluster creation, the administrator changed the HTTP port of the second cluster member to 9081.
Testing the servers using the snoop servlet directly to the server's HTTP port, the administrator got the following error message for the second server:
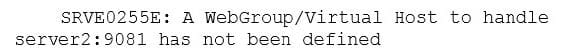
How can the administrator fix this problem?
A. Regenerate and propagate the HTTP plug-in.
B. Add the port 9081 to the default_host alias.
C. Create a new virtual host alias at the cell level for the port 9081.
D. Edit the server.xml for the second server and add the port 9081.
A WebSphere system administrator needs to install the Installation Manager (IM) on an unmanaged node on a host named
What step must the administrator take before submitting a job from the Integrated Solutions Console (ISC) to install the IM on
A. Install a node agent on
B. Install the job manager on
C. Start the job manager on
D. Register
A system administrator has been asked to uninstall an application from a cluster running in a WebSphere Application Server Network Deployment cell. This application was installed from the Integrated Solutions Console (ISC). The monitored directory for the cluster is
What step(s) can the administrator perform to uninstall the application?
A. Delete the application file from
B. Stop the running cluster.Delete the application file from
C. Stop the running cluster.Copy the application file to
D. Create a properties file to describe the deletion of the application file.Copy the properties file to
A system administrator wants to learn some of the Python scripting commands for the administration of the environment.
Which product feature should the administrator use?
A. The wsadmin.properties file to load a profile.
B. The AdminTask object to generate wsadmin scripts.
C. The guided activities panel from the Integrated Solutions Console (ISC).
D. The "Log command assistance commands" option in the Integrated Solutions Console (ISC).
A system administrator needs to configure a JDBC provider and a data source for an application in a clustered environment. The administrator also needs to copy the JDBC drivers from the database server to the application server machines.
How can the administrator meet these requirements?
A. Create a JDBC provider and the data source in the cluster scope.Copy the driver to all nodes.Set the environment variable at the node level to the driver's path.
B. Create a JDBC provider in the server scope and the data source in the node scope.Copy the driver to all application servers.Set the environment variable at the node level to the driver's path.
C. Create a JDBC provider in the node scope and the data source in the cell scope.Copy the driver to the deployment manager.Set the environment variable at the server level to point to the deployment manager path.
D. Create a JDBC provider in the application scope and the data source in the server scope.Copy the driver to all application server directories.Set the environment variable in each JVM to the driver's path.
A system administrator is configuring the security of a new environment. The administrator has been asked to configure one LDAP server that has different sub-trees for business users and administration users.
What should the administrator do to implement the required security configuration?
A. Install and configure a TAI (Trust Association Interceptor)
B. Configure a security domain for the stand-alone LDAP server.
C. Use Federated repositories and configure the supported entity types.
D. Use Stand-alone custom registry and configure the flat file implementation.
A system administrator has created a Jython script called globalScript.py.
What should the administrator do to ensure globalScript.py is loaded when the wsadmin shell is used?
A. Compile globalScript.py to a Java class in the bin directory.
B. Invoke wsadmin with the argument -profileName globalScript.py.
C. Modify the configureCustomProperty script to import globalScript.py.
D. Set the script profiles in the wsadmin.properties file to load globalScript.py.
A WebSphere Application Server cell was configured with a deployment manager node and a custom node. An operator manually changed some configuration files in the custom node, and the node became out of synch with the master repository.
The system administrator used the Synchronize button in the system administration session of the Integrated Solutions Console (ISC) to try to resynchronize the node, but the node remained out of sync.
What should the administrator do to fix it?
A. Use the Full Resynchronize button.
B. Invoke "sync" operation on NodeSync MBean.
C. Recreate the custom profile with the same name without deleting the node.
D. Manually copy all the deployment manager configuration files to the custom node.
A customer has enabled LTPA as their authentication mechanism and has web resources that are not secured by proper security constraints. A system administrator is required to ensure that all web resources are secured.
How should the administrator accomplish this?
A. Enable "Authenticate when any URI is accessed".
B. Enable "Authenticate only when the URI is protected".Disable "Use available authentication data when an unprotected URI is accessed".
C. Enable "Authenticate only when the URI is protected".Enable "Use available authentication data when an unprotected URI is accessed".
D. Map the application security roles to the configured user registry's groups.
A system administrator runs a Jython script that creates and configures several servers and realize that the script fails before completing. Although many tasks succeeded, they are rolled back when the script fails.
Before running the script again, what can the administrator add to the script after each task so the completed tasks are committed even if other tasks fail?
A. AdminApp.update()
B. AdminConfig.save()
C. AdminControl.invoke(server, `sync')
D. AdminTask.backupJobManager(`server')